This page gives a general idea on how authentication is plugged into the platform.
Authentication and user management is very pluggable so that the Nuxeo Platform can:
- Integrate with a Single Sign On system,
- Integrate with an external source of users and groups,
- Integrate easily any specific business logic tied to user management.
For that the Authentication and Identity services are separated in several components that can all be configured.
Actors in Authentication and Identity management
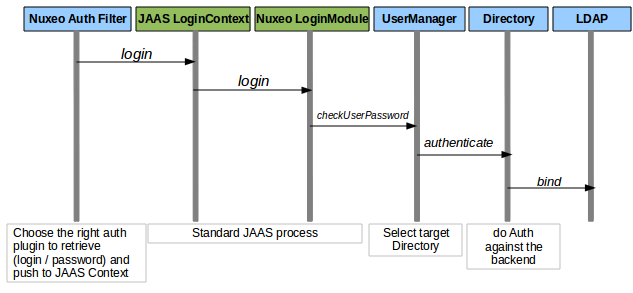
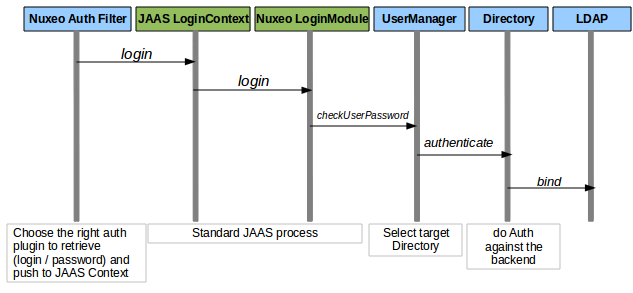
The different authentication and identity management actors are:
- Nuxeo Authentication Filter It protects HTTP access to Nuxeo resources. It will select and use Authenticator to retrieve credentials (login/password, certificate ...). It pushes identity in JAAS Stack.
Nuxeo Authenticators These are pluggable modules that encapsulate the logic for getting user's creadentials.
- They use HTTP Basic Auth.
- They display a Login/Password form.
- They redirect to a SSL server and then retrieve a token.
JAAS and Login Module This is the standard Java Security framework. The default LoginModule uses a LoginModulePlugins to do the credential validation. The default LoginModule Plugin will delegate credential validation to the UserManager.
UserManager This is the service responsible for managing Users and Groups. The underlying storage are accessed via the Directory API indirection.
- Directories Directories provide access to users and groups via LDAP, SQL or any custom implementation. They also provide a validated API to validate the credential against the user source.
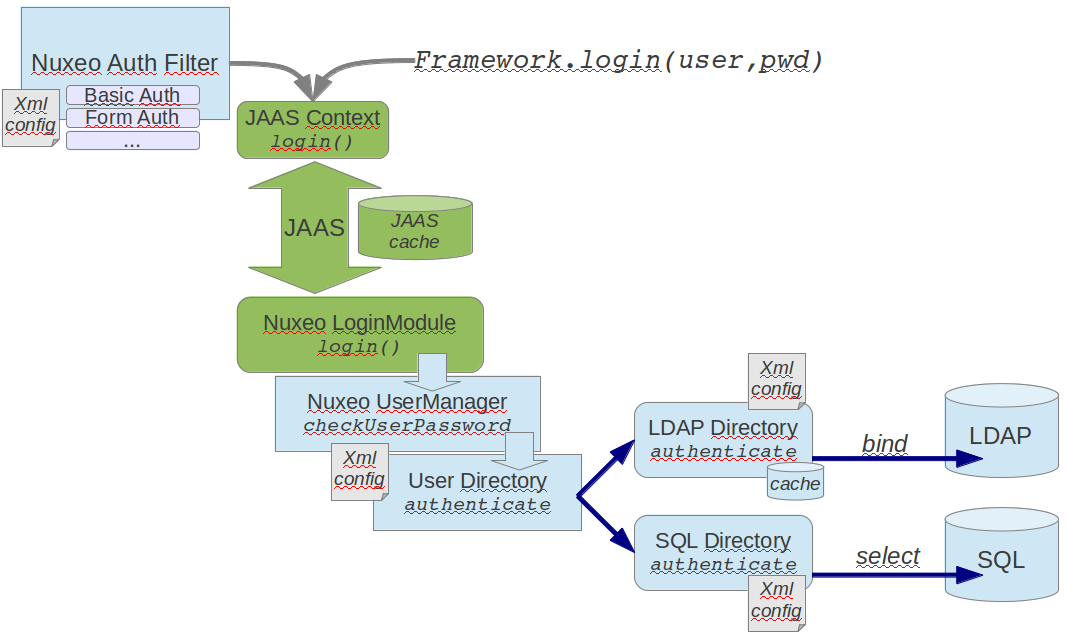
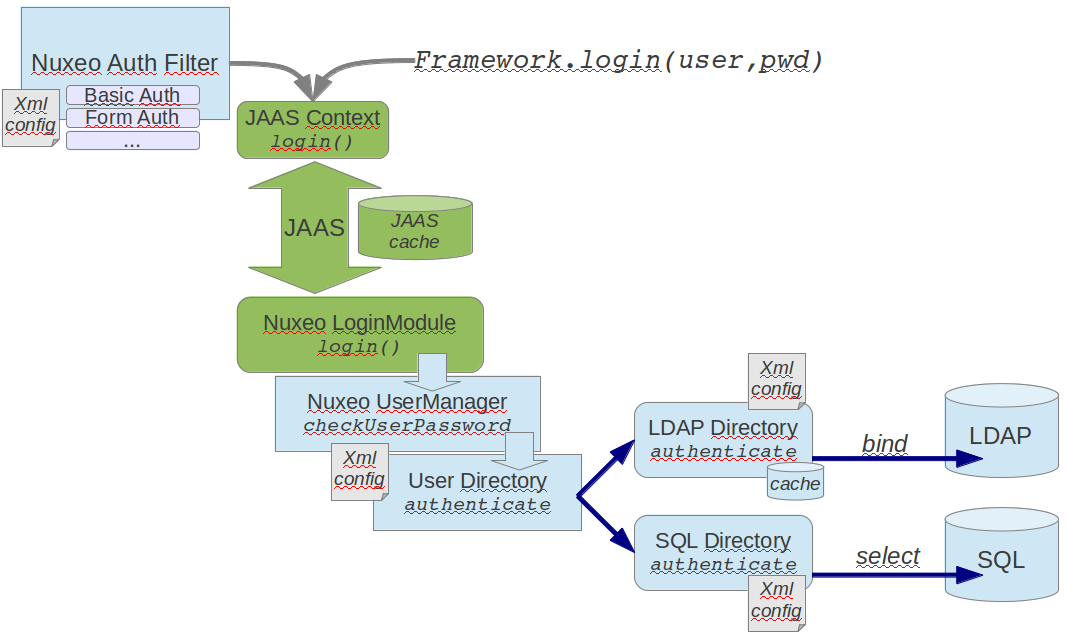
The initial identification can be done at Java level via JAAS or at HTTP level via a dedicated filter. The filter is pluggable so that the way of retrieving credentials can be an adapter to the target system. The JAAS login module is also pluggable so that you can define how the credentials are validated. By default, credentials are validated against directory that use LDAP, SQL or an external application.
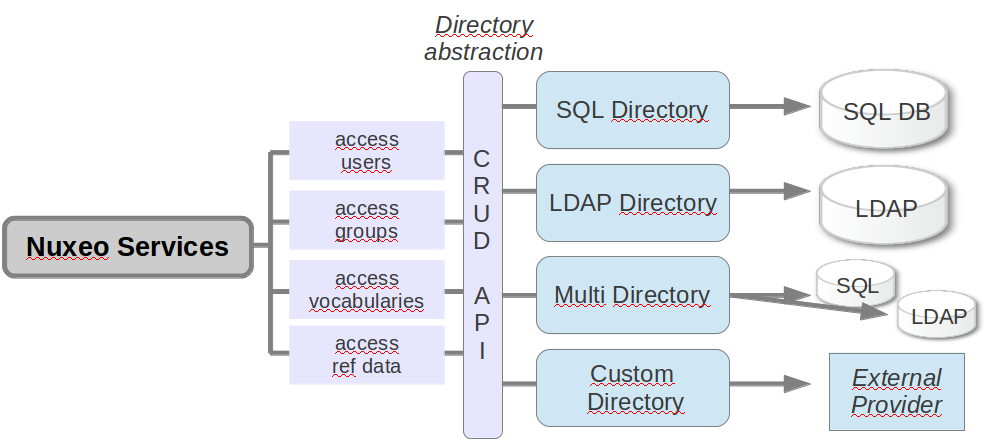
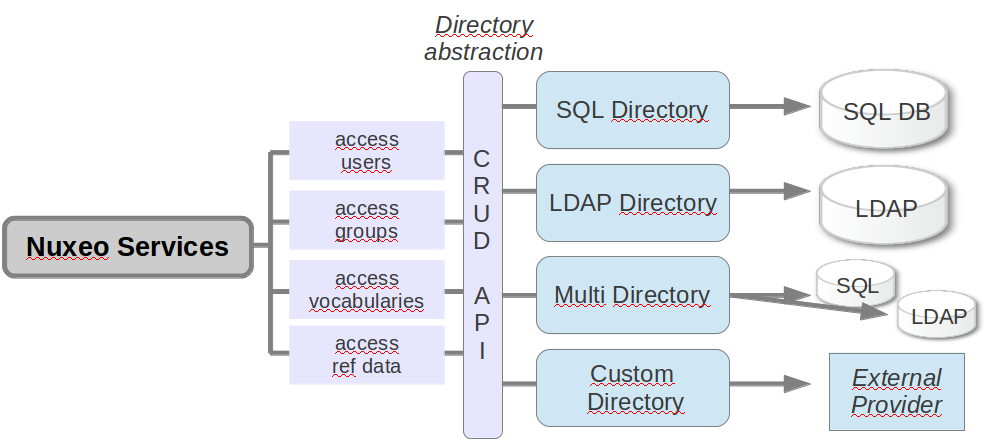
About the Directory Abstraction
The default LoginModule will delegate Authentication the UserManager that, by default, will delegate this to Directories.
Directories will be used to:
- validate user credentials,
- retrieve user information,
- retrieve groups.
The actual directory implementation can be:
- SQL,
- LDAP (use a LDAP bind for authentication),
- Multi-Directory (wrap several directories in once),
- Custom (ex: wrap a WebService ).
SSO Integration Strategies
In the case of SSO integration, the user will be authenticated by a third party service and Nuxeo should only:
- verify that the user has indeed been authenticated,
- retrieve information.
It means that at UserManager level, the validateUserPassword won't be called: UserManager will just check that the user exists so that a Principal can be created for the JAAS stack.
This explains why in most SSO plugin configuration, the target LoginModulePlugin is TrustedLM: Trusted = no need to validate credential, the SSO server already did it.
Integrating a Ticket Based SSO Server
The Authenticator plugin will be in charge of:
- redirecting the user to the SSO server if needed;
intercept the ticket:
- validate it against the SSO server,
- retrieve information about the user;
The resulting identify will be pushed to JAAS Stack.
CAS is a typical example of such an integration.
Integrating a Proxy SSO Server
In this case the Authenticator plugin will:
- check for a given header in the HTTP request;
- decrypt and validate the header token against the SSO server;
The resulting identify will be pushed to JAAS Stack.
Portal SSO is a typical example of such an integration.
Creating Users on the Fly
For some use cases, you may need to create users on the fly on the Nuxeo Platform side.
You can do this from the Authenticator which, after getting user information from the external server, can create the corresponding entry using the UserManager.
Shibboleth is a typical example of such an implementation.
Integrating SAML
CAS Server can work with SAML using additional module so this is one option.
The other option is to simply build a SAML Authenticator for Nuxeo: currently there is none available by default because no one asked for it and no one contributed one (even if we now that some projects have done this work).
Integrating with a Webservice Based Identify Provider
You can build a custom directory that will wrap your webservice.
You can use this sample as a starting point.
Authentication, users and groups Using Shibboleth Configuring User & Group Storage and Authentication