Functional Overview
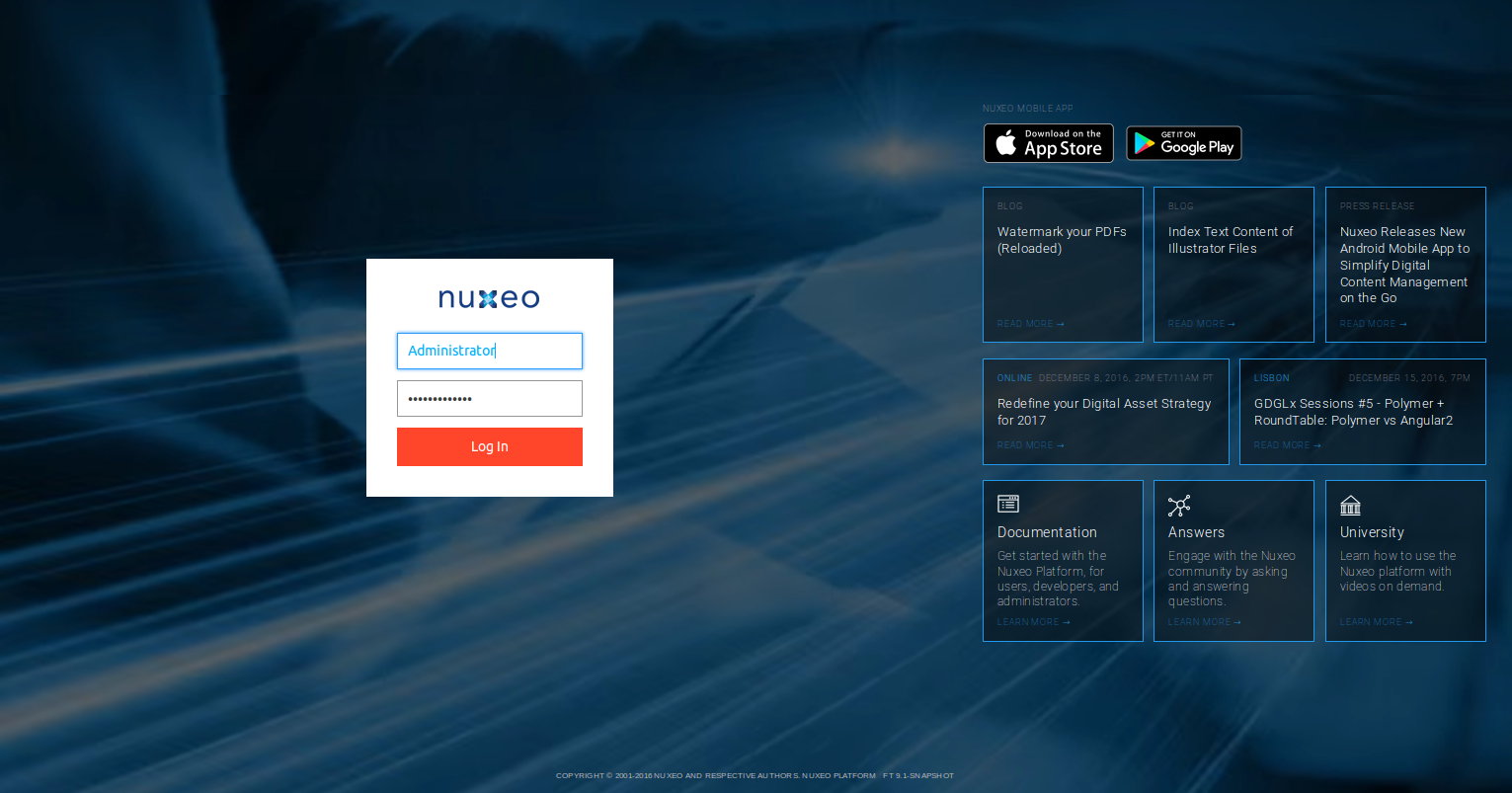
Default Authentication Mode - Login Page
By default, users get authenticated on the Nuxeo Platform by filling in their username / password on the login page. That information is checked against the one stored in the database, or transmitted to the configured identity provider. If the username or the password is invalid, a message is sent to the user. Default password of user Administrator is Administrator, if you didn't change anything. Password of each user can be changed either by the user themself, or by the administrators in the Admin Center. The password complexity is checked against a regex that can be changed.
Other Authentication Protocols
The login page is not the only way to authenticate a user against the Nuxeo Platform. Some other protocols can be used, sometimes requiring to install an additional module (see related pages):
- Basic Authentication (built-in)
- Token Authentication (Nuxeo Platform proprietary) (built-in)
- OAuth 2 (built-in)
- SAML 2.0 (addon)
- Two-Factor, with SMS for instance (addon)
- Trusted (for instance requests coming from a given IP address do not need to go through authentication) (built-in)
- OpenID (addon)
- Kerberos (built-in)
- CAS / CAS 2.0 (built-in)
- NTLM (built-in)
- Redirecting to a remote identity management solution then having the authenticated user be redirected to the Nuxeo Platform (SSO servers, OpenID, Portals, ...) (built-in or addon, depending on the case).
Thanks to the pluggability of the authentication layer (see the Authentication Chain Principles, it is easy to write a custom authentication protocol when necessary.
Compatible IdM Solutions
The default configuration checks identity against an SQL or DBS based directory. By configuration and addition of some modules, and following the above list of supported protocols, the Nuxeo Platform can be integrated with various identity providers:
- LDAP
- Active Directory
- OpenID compatible web platforms: Google, Twitter, Facebook, GitHub, ...
- SAML compatible identity management solutions, on premise or SAAS, such as OneLogin, ClearTrust, ...
- Kerberos compatible identity providers
- Shibboleth (Federated Identity Management)
- SSO Server (ex: CAS Server, Site Minder)
Unauthenticated Access
Anonymous User
A configuration allows to have the user automatically logged in as an anonymous user, for which some specific permissions have been set. The name of that user is configurable, and allows to simulate an "unauthenticated" access to the Nuxeo Platform. The users having the Everything permission on a repository can reference that anonymous user as any other user and declare some folders and documents accessible to everybody.
See the page Anonymous Authentication.
Unauthenticated URLs
It is also possible to define a list of URL patterns for which no authentication is required (so not using the anonymous user either). That way you can say that a specific website generated by the platform is available without authentication while the other pages served by the platform redirect the user to the login page. When browsing those URLs, no Principal object is created, which means no access to the repository can be done.
User and Groups Provisioning
Storage Options for Users and Groups
The UserManager is the component in charge of managing users and groups. The default implementation stores them in the Nuxeo Platform via the "directory" abstraction: one directory for users and one for groups.
Directories can use either:
- An SQL implementation (thus storing users and groups on the underlying RDBMS).
- A DBS implementation.
- An LDAP implementation.
- A Nuxeo Platform repository implementation (Users and Groups are then "documents") (not production-ready).
- A custom implementation for calling remote web services can also be used.
It is possible to reference a meta-directory that would be the result of the merge of several directories, a mix of different implementations (LDAP, SQL...) and different hosts. For instance, part of the users can be handled in the corporate LDAP server, and part in the Nuxeo Platform database. This situation is referenced as Multidirectory in the documentation.
Features Available Around Users and Groups Management
When users are dealt with through the directory abstraction (so 90% of the cases), the Nuxeo Platform provides user interfaces (and REST APIs) for handling:
- User CRUD by administrators.
- User password management by administrators.
- Group CRUD and assignment by administrators (including management of sub-groups).
- User profile management by the user.
- Password management by the user.
- User and group search (for filling in a metadata, assigning an ACL, selecting a specific user in a search filter,...).
- Nuxeo Platform User Registration: a Nuxeo addon that adds to the default Nuxeo Platform UI and services for inviting by email an external user.
For more information, please see Managing Users and Groups.
Virtual Users
It is also possible to declare a set of "virtual" users that are defined in the application although they don't exist in the user directory the Nuxeo instance is plugged to.
User Profile
A set of properties is stored by default for any user in the Nuxeo Platform:
- Username
- First name
- Last name
- Company
Those properties can come from the IdM the Nuxeo Platform is integrated to. To extend the list of available fields for a user, see the page How to Add New Fields to The User Profile or Group Profile.
Authentication Chain Configuration
You may want to use other authentication protocols and / or identity providers than LDAP/Active Directory. Most of the time, an "authentication plugin" has to be configured. The Nuxeo Platform provides some by default, but you sometimes have to install a specific addon.
In any case, you have to configure the "authentication chain", see the Authentication Chain Principles
Contribute an XML extension from the following content. Adapt the authenticationChain element content with the list of plugins you want to use.
<extension
target="org.nuxeo.ecm.platform.ui.web.auth.service.PluggableAuthenticationService"
point="chain">
<authenticationChain>
<plugins>
<plugin>BASIC_AUTH</plugin>
<plugin>ANONYMOUS_AUTH</plugin>
<plugin>THE_PLUGIN_I_WANT_TO_USE</plugin>
</plugins>
</authenticationChain>
</extension>
The Nuxeo Platform will use the plugins in the order they are chained up until one is successful. The first goal for each plugin is to retrieve an identity with the handleRetrieveIdentity method. If no identity is found, the plugin calls the handleLoginPrompt method.
Customization
Customizing the Login Page
You can customize the login page using Nuxeo Studio (background picture, colors, logo).
Integrating with a Web Service Based Identify Provider
You can build a custom directory that will wrap your webservice.
You can use the Nuxeo Directory Connector sample as a starting point.